

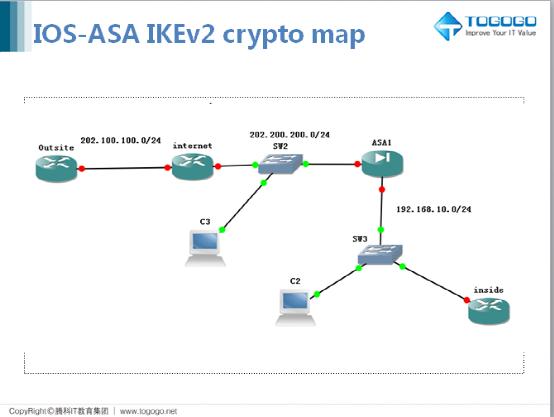
发布时间: 2017-06-16 11:33:57
配置ikev2 proposal (相当于之前v1时多个policy的集合,也可以做多个)
Outsite(config)#crypto ikev2 proposal ikev2-proposal
Outsite(config-ikev2-proposal)#encryption 3des aes-cbc-256
Outsite(config-ikev2-proposal)#integrity sha256 sha512
Outsite(config-ikev2-proposal)#group 2 5 15
策略中调用 proposal
Outsite(config)#crypto ikev2 policy ikev2_policy
Outsite(config-ikev2-policy)#proposal ikev2_proposal
Ikev2 key配置
Outsite(config)#crypto ikev2 keyring ikev2_key
Outsite(config-ikev2-keyring)#peer asa //只有标识意义
Outsite(config-ikev2-keyring-peer)#address 202.200.200.2
Outsite(config-ikev2-keyring-peer)#pre-shared-key cisco
配置ikev2 profile
Outsite(config)#crypto ikev2 profile ikev2_profile
IKEv2 profile MUST have:
1. A local and a remote authentication method.
2. A match identity or a match certificate statement.
Outsite(config-ikev2-profile)#authentication remote pre-share
Outsite(config-ikev2-profile)#authentication local pre-share
Outsite(config-ikev2-profile)#keyring local ikev2_key //调用key
Outsite(config-ikev2-profile)#match identity remote address 202.200.200.2 255.255.255.255 //对端地址
Outsite(config-ikev2-profile)#identity local address 202.100.100.1 //本地端点地址
配置ipsec 转换集
Outsite(config)#crypto ipsec transform-set myset esp-3des esp-sha-hmac
Outsite(cfg-crypto-trans)#mode tunnel //思科设备可协商
配置 crypto map
Outsite(config)#access-list 100 permit ip 192.168.1.0 0.0.0.255 192.168.10.0 0.0.0.255
Outsite(config)#crypto map mymap 1 ipsec-isakmp
Outsite(config-crypto-map)#set peer 202.200.200.2
Outsite(config-crypto-map)#set transform-set myset //可配置调用多个
Outsite(config-crypto-map)#set ikev2-profile ikev2_profile
Outsite(config-crypto-map)#match address 100
调用map
Outsite(config)#int f0/0
Outsite(config-if)#crypto map mymap
ASA
配置启用IKEv2
ASA(config)# crypto ikev2 enable outside
建立ikev2 策略
ASA(config)# crypto ikev2 policy 10
ASA(config-ikev2-policy)# encryption aes-256 des
ASA(config-ikev2-policy)# integrity sha256 sha
ASA(config-ikev2-policy)# group 2 1
ASA(config-ikev2-policy)# prf sha256 sha //注意默认策略匹配
配置tunnel-group
ASA(config)# tunnel-group 202.100.100.1 type ipsec-l2l
ASA(config)# tunnel-group 202.100.100.1 ipsec-attributes
ASA(config-tunnel-ipsec)# ikev2 local-authentication pre-shared-key cisco
ASA(config-tunnel-ipsec)# ikev2 remote-authentication pre-shared-key cisco
配置IKEv2 proposal
ASA(config)# crypto ipsec ikev2 ipsec-proposal ikev2_proposal
ASA(config-ipsec-proposal)# protocol esp encryption 3des
ASA(config-ipsec-proposal)# protocol esp integrity sha
感兴趣数据流
ASA(config)# access-list 100 permit ip 192.168.10.0 255.255.255.0 192.168.1.0 255.255.255.0
配置crypto map
ASA(config)# crypto map mymap 1 match address 100
ASA(config)# crypto map mymap 1 set peer 202.100.100.1
ASA(config)# crypto map mymap 1 set ikev2 ipsec-proposal ikev2_proposal
ASA(config)# crypto map mymap interface outside //调用
注意:ASA没有默认策略集,修改配置需要和ios端匹配
上一篇: {思科CCNP-RS}BGP 路径选择